Mission `Freshly` VM : I downloaded the virtual machine hosted at https://www.vulnhub.com/entry/tophatsec-freshly,118/ . There are a couple of challenges from TopHatSec and I would like to try them both. Well for starters here is `Freshly` :-)
Detailed steps for getting root :
A nmap scan of the box reveals that ports 80,443 and 8080 are publically accessible on the box.
We quickly run both nikto and dirbuster against the webserver. We see that the VM is running a login application on port 80 while on the other ports it is running a wordpress blog.
We also see an installation of phpmyadmin on the webserver. We try the default credentials but dont succeed. Since there is a phpmydamin running on the box we guess that there may be mysql server running at the backend as well. Hence we try mysql authentication bypass by using a wronguser' or 1=1 LIMIT 1;# as username and junk as password. However we are not successful. Inspite of this its worth the effort to run sqlmap against the server to see if it can pick up some injection points either in the username or password fields.
Sqlmap tells us that the `user` parameter of the login form is sucesptibel to a mysql injection vulnerabilty. It readily exploits this vulnerability for us to give us a complete dump of the database when we use the --dump sqlmap option.
Excellent! now we can see that there are a total of 7 databases in the database. We must check out the interesting ones especially login, phpmyadmin, users and wordpress8080.
It seems that the table dump for the wordpress8080 database contains the admin password for the wordpress blog. We try to login to the wordpress blog via the credentials and we are successful!
Once we have admin credentails on the wordpress getting a shell on the box is extremely simple. By default wordpress will not allow any php content to be run from the wordpress articles/posts. However since we have admin privs on the wordpress we can install a plugin called Exec-php to allow php code to run in the wordpress pages.
We install the plugin to our wordpress installation and then follow the instructions at https://wordpress.org/plugins/exec-php/installation/ to run php code in the article body. Once the simple php hello world example works we use the php-reverse-shell script available at http://pentestmonkey.net/tools/web-shells/php-reverse-shell . We set up a netcat listener and sure enough we get our shell :-)
There we have our flag. A fun challenge indeed :-)
Detailed steps for getting root :
A nmap scan of the box reveals that ports 80,443 and 8080 are publically accessible on the box.
We quickly run both nikto and dirbuster against the webserver. We see that the VM is running a login application on port 80 while on the other ports it is running a wordpress blog.
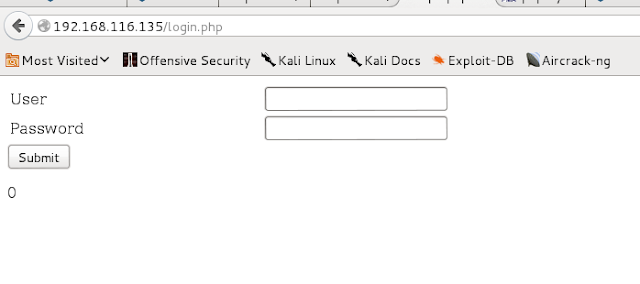 |
| Login prompt |
 |
| Wordpress blog |
Sqlmap tells us that the `user` parameter of the login form is sucesptibel to a mysql injection vulnerabilty. It readily exploits this vulnerability for us to give us a complete dump of the database when we use the --dump sqlmap option.
Excellent! now we can see that there are a total of 7 databases in the database. We must check out the interesting ones especially login, phpmyadmin, users and wordpress8080.
It seems that the table dump for the wordpress8080 database contains the admin password for the wordpress blog. We try to login to the wordpress blog via the credentials and we are successful!
Once we have admin credentails on the wordpress getting a shell on the box is extremely simple. By default wordpress will not allow any php content to be run from the wordpress articles/posts. However since we have admin privs on the wordpress we can install a plugin called Exec-php to allow php code to run in the wordpress pages.
We install the plugin to our wordpress installation and then follow the instructions at https://wordpress.org/plugins/exec-php/installation/ to run php code in the article body. Once the simple php hello world example works we use the php-reverse-shell script available at http://pentestmonkey.net/tools/web-shells/php-reverse-shell . We set up a netcat listener and sure enough we get our shell :-)
There we have our flag. A fun challenge indeed :-)


No comments:
Post a Comment